Akamai has noticed that attackers are using the little-known DCCP network protocol (Datagram Congestion Control Protocol) for DDoS attacks.
This internet standard was approved in 2007 and helps monitoring network congestion for UDP-based communications. DCCP is especially effective for applications where data arriving at the wrong time becomes useless. For example, streaming, online gaming, and Internet telephony.
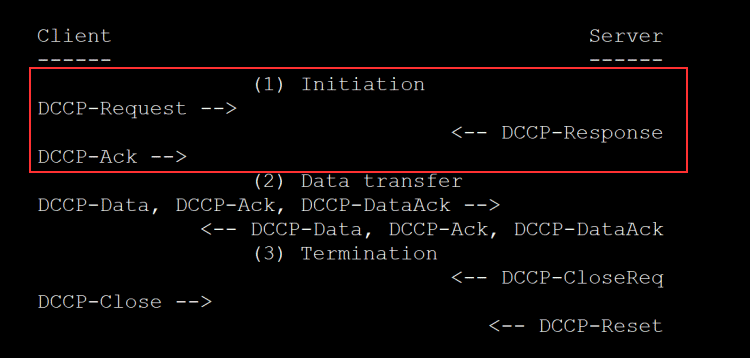
Although the protocol includes many features, Akamai reports that hackers abuse the three-way handshake that occurs at the start of a DCCP + UDP connection. Thus, attackers can send a stream of DCCP-Request packets to port 33 of the server (where the DCCP protocol works), thereby forcing the server to spend important resources on initiating multi-way three-way handshakes that will not complete, and will eventually disable the server (due to lack of available resources).
This attack is similar to the TCP SYN flood, a well-known type of DDoS attack that has been used in a similar way for over a decade.
The specialist emphasizes that even if the DCCP three-way handshake is completed, and the server “survived” the flood of packets, attackers can still abuse UDP packet spoofing and simply use the open ports of the DCCP server to repel and amplify attacks on third-party services.
Fortunately, even though the protocol has been around for almost 14 years, very few OS and application developers have bothered to support it. For example, some Linux distributions ship with DCCP support, but not all Linux distributions ship with DCCP sockets enabled out of the box. Windows systems do not seem to support this protocol at all, which explains the reluctance of some application makers to add it to their software.
That is, Akamai believes that such attacks cannot present significant harm. However, this may change if the protocol becomes more popular in the future as real-time streaming becomes more common.
As a result, Siman recommends blocking all port 33 traffic just in case, especially in an infrastructure where DCCP is not used but is supported.
Let me remind you that I recently reported that DTLS can amplify DDoS by 37 times.