Norton scam email is a tricky phishing campaign that pretends to be an official mailing from Norton. It generally aims at users’ sensitive information, including banking data. Let’s figure out what these spam emails are, how dangerous they are, and how you can counteract them.
What is Norton Scam?
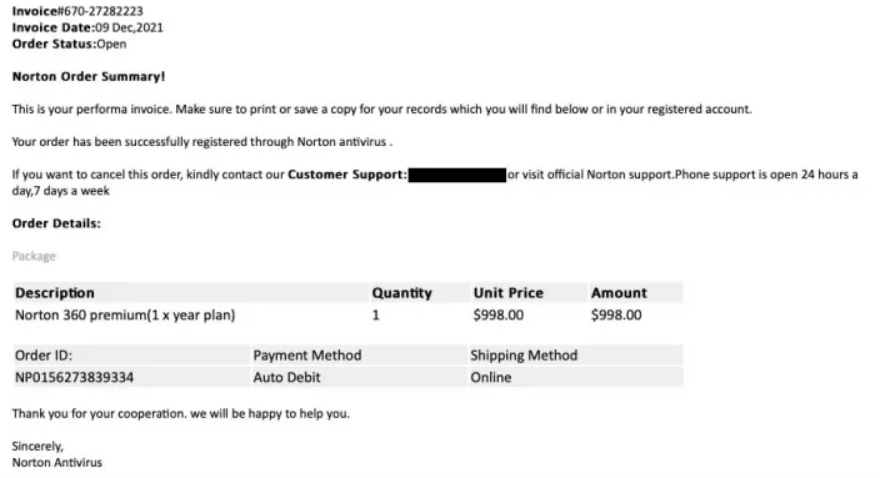
Norton scam email is a common name for dubious emails that may come to anybody, regardless if they are the users of their products or not. These emails may potentially contain different text and disguise, same as any other phishing. But the most common is a notification about the subscription purchase or renewal. People receive a message that says their card was charged with a hefty sum, and to cancel it and receive a refund you should follow the instructions. The sum varies from $200 to $1000. This is not very realistic as these emails usually come to single users, who will never buy a corporate license or a one for 10+ machines.
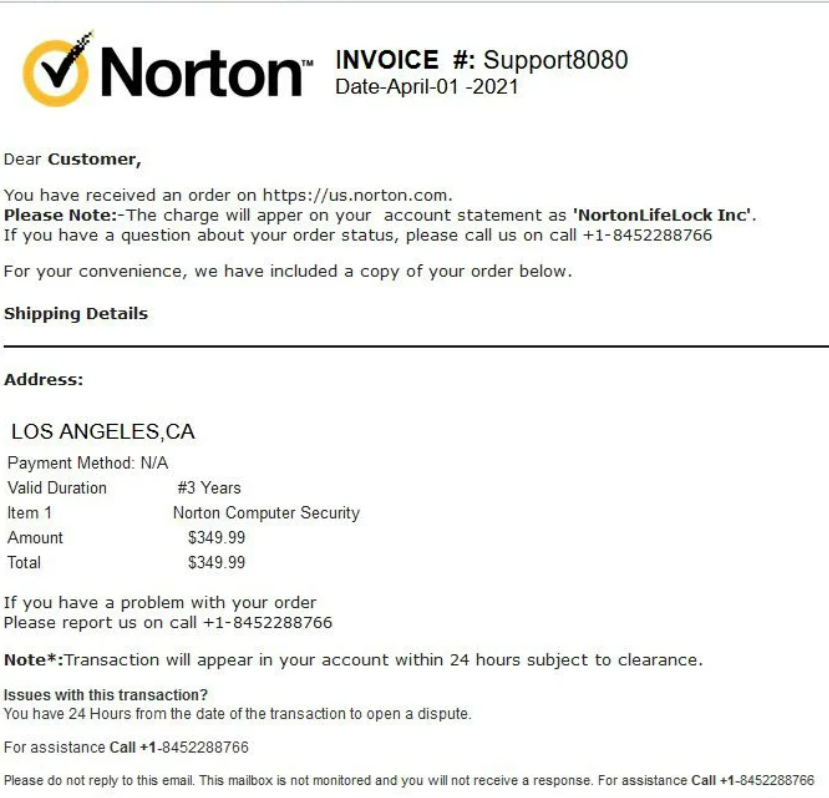
Still, the sum is pretty scary and attracts the user’s attention. Phishing Norton emails may occasionally contain a link to a third-party site or a contact number of tech support. Both of them, as you can already guess, have nothing to do with the real services of a company. Villains may use a single phishing page for multiple spam campaigns.
The link may be plain text, as well as inside of the button or email text. It leads you to a phishing page, that will ask for your personal information – name, email address, phone number, et cetera. In some cases, they can ask you about the bank card details, including the security code (CVV/2). Later, this information will be used against you – after selling it to a third party on the Darknet.
The Tech support number is no good as well. There, crooks who mimic the real support will try to lure out your sensitive information, same as in the case with a link. The other thing which repeats the previous method is the behavior around the collected data – they sell it on Darknet forums as well.
How dangerous is the Norton scam email?
Same as any other phishing, it aims at grabbing as much personal information as possible. At a glance, you may think it is not that bad, as you share this information with different online services too. However, most of them keep this data a secret, as there are data protection laws that punish data selling. Meanwhile, phishing actors are not bound by any kind of laws, as the very essence of phishing is outlawed.
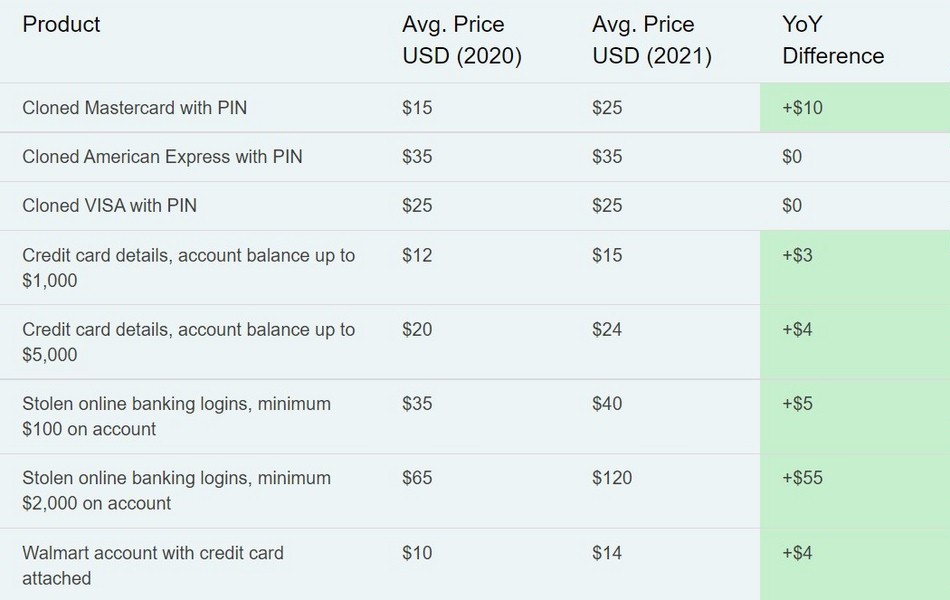
It is unlikely to meet a benevolent person among the buyers for leaked information on the Darknet. If you’ve shared your personal information, that will be the base for more precise, spear phishing. Crooks will try to perform a more sophisticated fraud to make you pay them by mimicking a thing you’re expecting. Leaked bank card details, on the other hand, give them the ability to manage your money as they want – and they can find a way to circumvent the bank’s safety measures. Carding has become way less widespread over the last 5 years, but remains a threat.
How to avoid being fooled with email scams?
There are a few rules that will help you to detect and avoid any questionable emails. They do not require anything specific and only rely on your attentiveness. Even the most sophisticated scams cannot be 100% identical to genuine emails. When it comes to some massive mailing with low-quality phishing emails, it is very easy to bust their disguise.
Unrealistic claims or offers
Do you really think Norton will charge you without your knowledge? Or offer a 1-year license for free, just for taking part in a quiz? When the things in the letter look untrustworthy, get some other ways to verify such offers. For example, you can check your bank account and see if there were any debit operations as described in the letter. On the official Norton website, you can see if there are any active subscriptions, and also promotions or giveaways. Still, emails may repeat the promotions, but contain a different link, so you will get into a fraud either.
Email addresses
No one can copy the email addresses of genuine mailing services, used by companies. And phishing actors sometimes don’t even try to – they apply using hijacked accounts or single-use emails, created only for spamming. Hence, seeing a letter that pretends to be a message from Norton, and is sent from [email protected] is already fishy. In advanced scams, crooks may try to spoof the genuine address by changing the letters with numbers, to make them harder to distinguish from real ones in haste. For example, you may witness the [email protected] instead of [email protected]. Here is the list of address domains used by Norton in their official mailing – crooks cannot use or counterfeit it in any way.
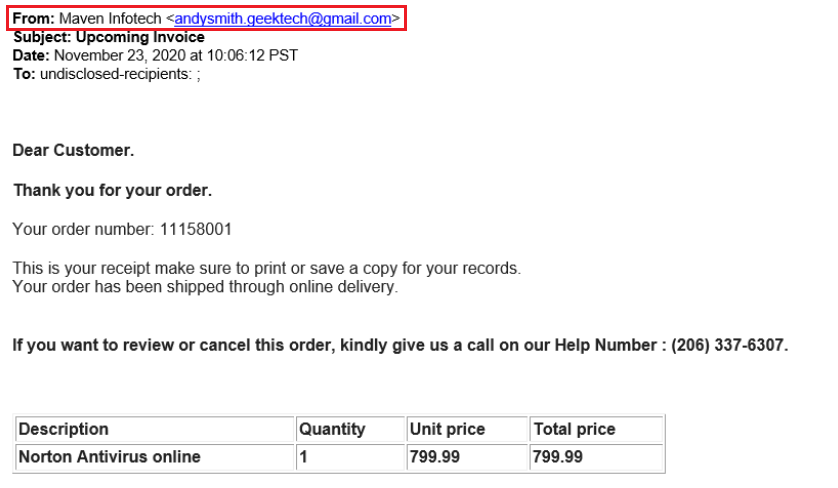
Typos and poor email design
Can you imagine official letters from a worldwide-known company, whose design is poor and the text is full of errors? Most companies hire several writers who review the patterns used for automated emails and check up on all hand-made correspondence. Seeing a genuine letter that looks like a kid’s scribble is hardly a case. Be sure that it is likely a scam; you can additionally confirm your expectations by looking for the signs we mentioned above.

Like