Cybersecurity experts once again warn that while pursuing for free games and applications, users face the risk of installing a malicious program that may collect all passwords in the system and send them to its operator. Cybercriminals increasingly use pirated software to deliver backdoors and ransomware.
Previously, fans of free applications mostly came across unwanted programs like adware or dubious extensions for browsers, but now everything is much more serious – there is a real danger of installing in the system ransomware and stealing passwords Trojans.
“It is quite logical that at some point the creators of the “cracks”and other similar tools for bypassing licensing restrictions decided to monetize their activities. As a result, many of them began working with developers of ransomware and password-stealers to help them distribute their malicious applications”, – write BleepingComputer reporters.
In other words, by installing a new game or licensed software for free, you risk, as your personal and financial data, as well as other confidential information, may fall into the hands of third parties.
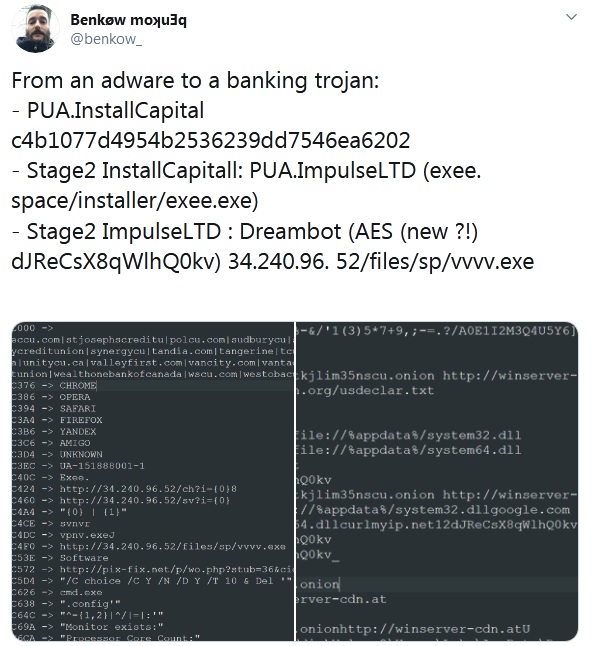
Security researcher Benkøw, who has recently studied this problem, claims that software cracks and key generators in most cases install stealing credentials Trojans and programs for remote access in the system.
Over the past week, Benkøw downloaded a variety of applications that as cheats for games, key generators, and hacked programs. Having installed them, the expert discovered that Trojans and backdoors “Dreambot, Glupteba and Racoon” “settled” in his system.
All these malicious programs give attackers full access to the infected computer.
“In the BleepingComputer tests, we were infected with ShadowTechRAT, which allowed an attacker to gain full access to the infected computer. It’s known that one of the most common ransomware programs, called STOP, is installed through these same ad packages”, – write BleepingComputer employees that ventured for an experiment to repeat Benkøw’s experience.
As a rule, “free” games and programs are hosted on torrent sites, fake resources, supposedly specializing in hacking software, and even on YouTube.
On torrent sites, it can be noted that the same user has downloaded many different games, applications and key generators of the same size.
“YouTube also has its share of scammers that create videos, advertising a cheat game, and then post a link to download the file. Like torrent sites, these downloads are adware packages that install malware”, – say the researchers.
While it may be tempting to download pirated software so you don’t have to pay for it, the risks far outweigh the rewards.
Even if to leave aside the fact that downloading copyrighted software is illegal, it’s just not worth the potential risk of identity theft in online banking or the loss of other data.
Recently, Danish information security experts studied the working methods of ransomware operators REvil (Sodinokibi), and learned that attackers demand hundreds of thousands of dollars from victims. Of course, this ransomware is more focused on large companies, but think about it – is it better for you to spend tens of dollars on legal software than thousands on ransom?
Well, the traditional advice is to use reliable anti-virus software.