Hackers published on the network an exploit for a zero-day vulnerability that is actively used in the GoAnywhere MFT administration console. Fortra, the company behind the GoAnywhere MFT, was forced to release an emergency patch to fix this bug.
Let me remind you that we also reported that Exploits for Vulnerabilities in Three Popular WordPress Plugins Appeared on the Network, and also that Thousands of GitHub Repositories Spread Malware That Is Disguised as Exploits.
The media also wrote that PoC Exploit for PlayStation 5 Appeared, but It Works Only in 30% of Cases.
GoAnywhere MFT is a file transfer tool designed to help organizations securely share files with partners and maintain audit trails of who has accessed shared files. Behind its creation is Fortra (formerly known as HelpSystems), which also develops the well-known and widely used Cobalt Strike tool, aimed at pentesters and the red team, and focused on operation and post-operation.
At the end of last week, well-known information security journalist Brian Krebs warned in his Mastodon that Fortra developers discovered an RCE exploit and attacks on the GoAnywhere MFT, after which they were forced to temporarily disable their SaaS service.
At the same time, the company’s official announcement stated that the exploitation of the vulnerability requires access to the administrative console, which under normal conditions should not be accessible via the Internet at all. However, Shodan detects about 1000 available GoAnywhere instances on the Internet (although only about 140 installations were seen on ports 8000 and 8001, which are the defaults used by the affected admin console).
The company reported (access to the bulletin is possible only for clients with an account) that the vulnerability is already being used in attacks. Fortra has listed indicators of compromise for potentially affected clients, including a specific stack trace that should appear in compromised system logs.
However, there was no fix at that time, and the developers offered users other ways to reduce risks. In particular, the security bulletin contained the following instruction:
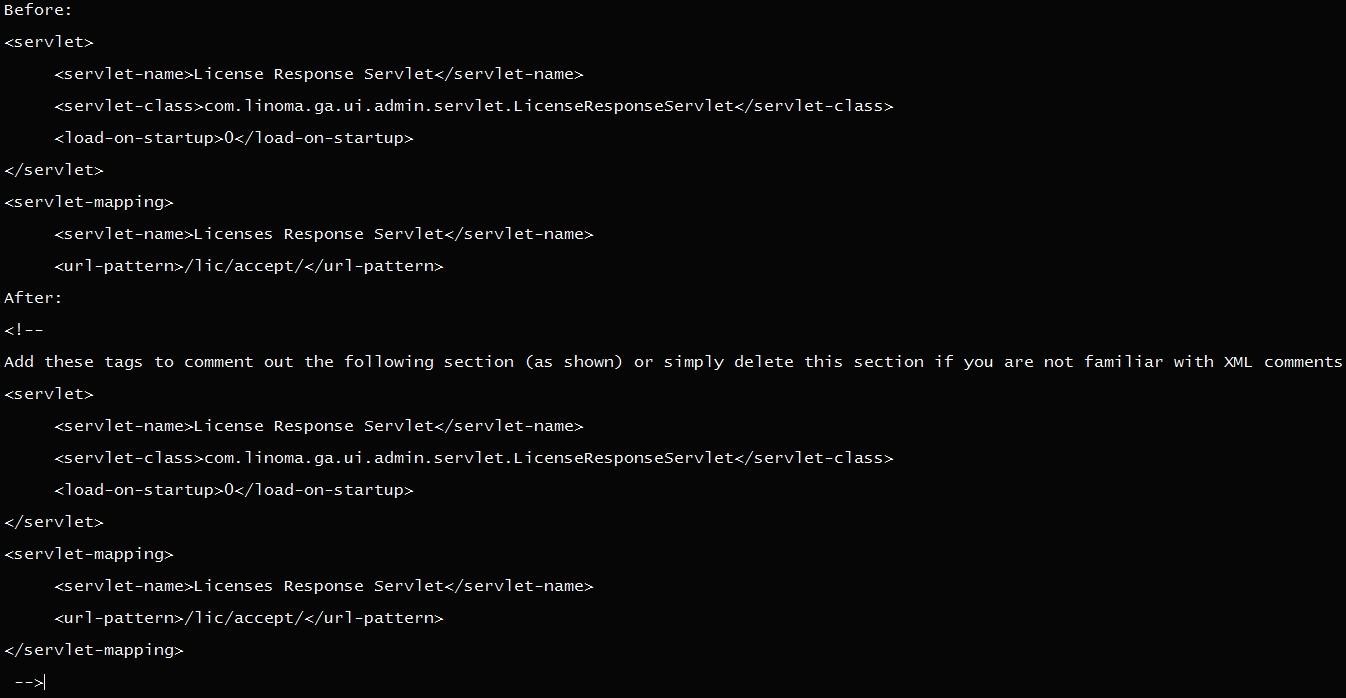
- on the file system where GoAnywhere MFT is installed, edit the file [install_dir]/adminroot/WEB_INF/web.xml;
- find and remove (remove or comment out) the servlet configuration and servlet mappings as shown in the screenshot below;
- restart GoAnywhere MFT.
Just a couple of days later, on Monday, researcher Florian Hauser from the security consulting company Code White released the technical details of the vulnerability in the GoAnywhere MFT and the PoC exploit code. According to him, the problem allowed remote code execution on vulnerable GoAnywhere MFT servers without authentication.
Today, on February 7, 2023, Fortra finally released an emergency patch for this 0-day vulnerability (7.1.2) and urged all customers to install it as soon as possible. The company emphasized that “customers using the administration portal available via the Internet” should take care of especially urgent installation of the fix.